With traditional security audits, organisations pay researchers even if they do not find any vulnerabilities. This makes it prohibitive to carry out continuous testing as required by today’s agile system development and deployment. Bug bounty programs are a revolutionary way of carrying out continuous testing within a set budget. Around the world, governments, BFSIs, fintechs, telcos, utilities, internet giants, e-commerce, retail and more have leveraged bug bounty to secure themselves from cyber threats. However, some common myths about bug bounty programs prevent organisations from experiencing their absolute value. Examples are:
✓ Can we trust the bug bounty hunters
✓ How are the hunters selected
✓ How does it differ from penetration testing
In this discussion, YOU get to ask the questions!
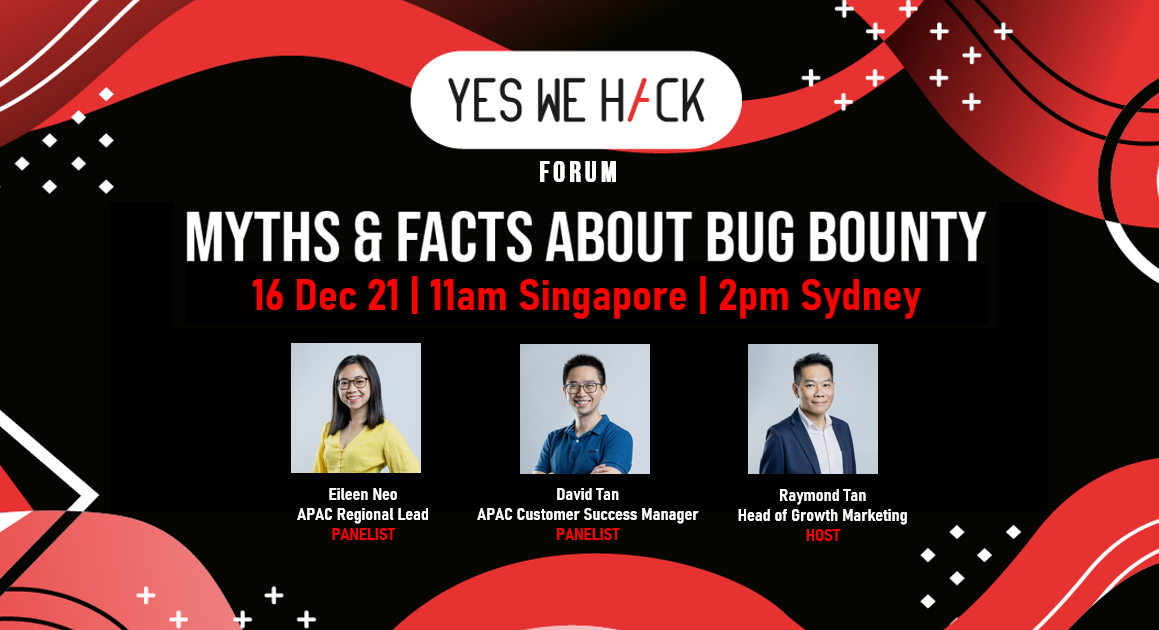
Our panelists, Eileen Neo, the APAC Regional Lead and David Tan, the APAC Customer Success Manager, have advised and implemented bug bounty programs for customers in Asia. The session will be hosted by Raymond Tan, Head of Growth Marketing.
Eileen Neo is the APAC Regional Lead for YesWeHack and helms all business development activities in the region. Backed by five years of serving the Singapore Police Force and six years of experience in the tech industry, Eileen has married her interests. She now focuses her efforts on fighting cybercrime in the digital world. Eileen is all about maintaining law and order in both the offline and online world!
David Tan is the APAC Customer Success Manager at YesWeHack. He helps customers navigate the challenges of vulnerability management and get the most value out of our services.
Raymond Tan is the Head of Growth Marketing at YesWeHack. He will be your host for the discussion.

-
Founded in 2015, YesWeHack is a Global Bug Bounty & VDP Platform. We connect organizations with more than 30,000 ethical hackers from 170 countries to secure their exposed scopes and report vulnerabilities in their websites, mobile apps, infrastructure and connected devices. Learn more here.