Are you curious about the inner workings of Bug Bounty programs and how vulnerabilities are identified, reported, triaged and fixed?
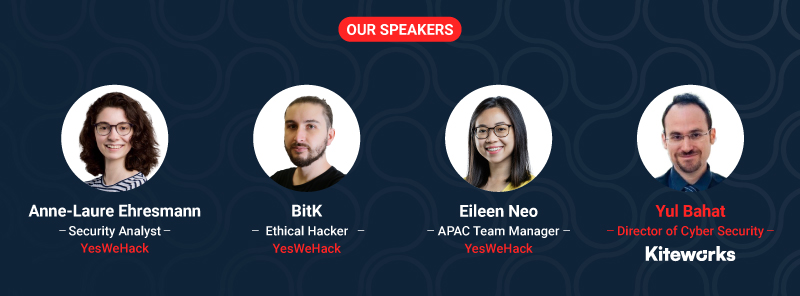
Join us on 11 April for a deep dive into the Bug Bounty journey in its most operational form. Our panel of experts from YesWeHack will be presenting, along with special guest Yul Bahat, Director of Cybersecurity at Kiteworks.
During this webinar, we'll delve into the operational aspects of Bug Bounty programs, examining the entire process from the ethical hacker's perspective to the final customer's perspective. You'll gain valuable insights into how vulnerabilities are identified, reported, and fixed, and learn about the key considerations involved in triaging and addressing security issues.
Don't miss this opportunity to deepen your understanding of Bug Bounty programs and the important role they play in ensuring software security.
Who should attend?
- CISO/CTO/ Head of IT departments
- Security professionals
- Anyone interested in learning about the process of detecting and fixing bugs, particularly within the context of a Bug Bounty program